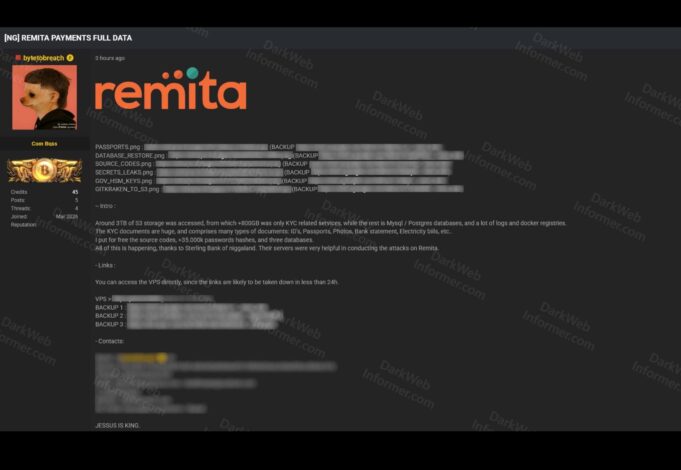
A massive cybersecurity incident has been reported involving Remita, Nigeria’s primary payment gateway and the technological backbone of the Federal Government’s Treasury Single Account. A threat actor using the alias “bytetobreach” claimed responsibility for the attack on dark web forums, alleging they exfiltrated approximately 3 terabytes of highly sensitive data.
The Scale of the Alleged Leak
According to posts shared by the threat actor, the breach originated from compromised Amazon S3 storage buckets. The leaked data reportedly includes 800GB of KYC documents — massive archives containing passports, photos, bank statements, and utility bills. Financial and technical records allegedly include full MySQL and Postgres databases, internal logs, and docker registries.
The claimed haul also encompasses intellectual property such as corporate source codes and configuration files containing API keys. User credentials form another disturbing component — over 35,000 password hashes and critical government Hardware Security Module keys that protect cryptographic operations.
The Sterling Bank Connection
In a provocative claim, bytetobreach alleged that Sterling Bank’s infrastructure facilitated the breach. The attacker stated that the bank’s servers proved “very helpful” in conducting the pivoting attacks required to compromise Remita’s systems. This assertion, if accurate, raises serious questions about the security posture of financial institutions connected to Nigeria’s critical payment infrastructure.
Sterling Bank has not issued any public statement addressing these allegations as of this writing.
Immediate Impact and Risks
The exposure of KYC data represents severe risk for both individual users and corporate entities. With access to passports and utility bills, malicious actors can execute sophisticated identity theft schemes, fraudulent loan applications, and highly targeted phishing campaigns. The leak of source code and HSM keys could provide a roadmap for future exploits against the platform’s payment processing logic.
Remita processes trillions of naira on behalf of the Federal Government through the Treasury Single Account, which consolidated over 17,000 government bank accounts. The platform handles everything from salary payments to tax collections across Ministries, Departments, and Agencies. A breach of this magnitude—if confirmed—could undermine public trust in Nigeria’s digital payment infrastructure.
No Official Confirmation Yet
SystemSpecs, the parent company of Remita, has not issued any public statement confirming or denying the breach. Neither the Central Bank of Nigeria, affected commercial banks, nor the Federal Government has released official comment on the incident.
This silence is concerning given Nigeria’s Data Protection Act 2023, which requires data controllers to notify the Nigeria Data Protection Commission within 72 hours of becoming aware of a breach that poses risk to individuals’ rights and freedoms. The law also mandates immediate communication to affected data subjects when breaches pose high risk.
The alleged incident comes during a period of heightened cybersecurity scrutiny in Nigeria. The country recorded over 119,000 data breaches in Q1 2025 alone, according to security reports. In February 2026, the Central Bank directed all deposit money banks to complete mandatory cybersecurity self-assessments within three weeks—a directive that now appears prescient given this alleged breach.
The ByteToBreach Pattern
The threat actor bytetobreach has emerged as a prominent figure in underground data markets since at least June 2025. Security researchers have linked the alias to multiple high-profile breaches targeting airlines, financial institutions, government agencies, and healthcare providers across several countries.
Previous targets attributed to bytetobreach include Sweden’s e-government infrastructure through CGI Sverige, Viking Line’s passenger databases, and Seychelles Commercial Bank’s customer records. The actor typically operates through dark web forums like DarkForums and uses encrypted communication channels including ProtonMail, Telegram, and Pastebin.
Security firm investigations suggest bytetobreach employs cloud infrastructure exploitation, credential reuse from infostealers, brute force attacks, and misconfiguration-based access to infiltrate targets. Once inside, the focus shifts to exfiltrating sensitive databases for sale or public leak.
Security Recommendations
While official confirmation from SystemSpecs remains pending, users are advised to take immediate defensive measures. Change passwords for all Remita-linked accounts and any other services sharing the same credentials. Activate Multi-Factor Authentication on all financial accounts and primary email addresses.
Monitor bank statements closely for unauthorized micro-transactions or suspicious mandates. If possible, notify your primary bank to place heightened security alerts on your accounts due to potential identity theft risk. Remain vigilant for phishing attempts that reference specific personal details—a hallmark of attacks following KYC data exposure.
What Comes Next
The Nigerian cybersecurity community is closely monitoring for official responses from SystemSpecs, the Nigeria Data Protection Commission, and the Central Bank. The alleged breach raises fundamental questions about cloud security practices, third-party risk management, and the security architecture protecting Nigeria’s critical financial infrastructure.
For a platform that processes government salaries, pensions, and tax collections affecting millions of Nigerians, transparency about what happened, how it happened, and what protections are being implemented is not optional—it’s legally mandated and essential for maintaining public trust.
Users should watch for breach notification letters, which the Data Protection Act requires data controllers to send to affected individuals in plain language, including advice about mitigation measures. Until official confirmation arrives, the prudent approach is to assume potential exposure and act accordingly.
Follow us on Bluesky, LinkedIn, X, and Telegram to Get Instant Updates