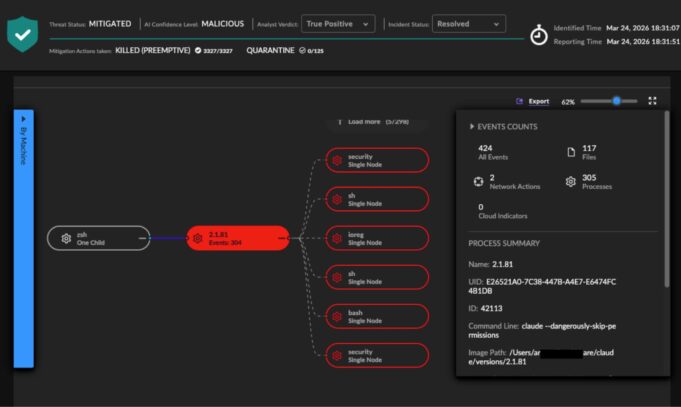
The compromise, detected by SentinelOne’s Singularity Platform, prevented significant damage across multiple customer environments. The attack leveraged malicious Python code and was identified and blocked autonomously on the same day it was launched, without requiring manual queries, SOC team triage, or signature updates. This demonstrates the necessity of machine-speed defense against rapidly evolving threats.
The Anatomy of an AI Supply Chain Compromise
The trojaned LiteLLM package, specifically versions 1.82.7 and 1.82.8, had been compromised hours before detection. This multi-stage, multi-surface attack was designed to evade traditional manual security workflows. According to SentinelOne, the attack involved several critical stages:
- Malicious Python Execution: The compromised package executed malicious Python code within affected environments.
- Data Theft & Exfiltration: The payload harvested secrets, including sensitive data from cloud platforms and SSH keys. All stolen data was encrypted with AES-256-CBC and exfiltrated to an attacker-controlled server.
- Persistence: On non-CI systems, the attackers installed a systemd user service to maintain a persistent backdoor, polling for second-stage payloads.
- Kubernetes Lateral Movement: The attack facilitated lateral movement within Kubernetes clusters, indicating an attempt to expand control and access sensitive resources.
This incident underscores the growing risk of AI supply chain attacks, where a compromised tool or component can lead to widespread impact.
Autonomous Defense: A New Security Imperative
SentinelOne asserts that host-based Behavioral Autonomous AI Detection is the most effective way to detect and stop both human and machine-speed AI agent-based malicious activities. The Singularity Platform’s AI-powered capabilities enable real-time threat detection and automated response across endpoints, cloud workloads, and identity.
This autonomous approach is crucial for bridging the gap between the velocity of modern cyberattacks and the capacity of human-driven investigations. As AI infrastructure becomes a prime target, organizations must adopt an architectural decision towards AI-native defense to secure their digital assets effectively.
What’s Unknown
Specific details regarding the number of affected customers or the exact impact on those environments beyond detection and blocking are not publicly available.
Follow Hashlytics on Bluesky, LinkedIn , Telegram and X to Get Instant Updates