A relatively new threat actor operating under the alias XP95 has claimed responsibility for breaching NNPC Health Maintenance Organisation, Nigeria’s state-owned health insurance provider. The group alleges they exfiltrated approximately 200,000 user records containing personal data from the organization’s systems, though the claim remains unverified as of April 8, 2026.
What Is NNPC HMO?
NNPC Health Maintenance Organisation Limited is a nationally accredited health insurance provider established to support the healthcare needs of NNPC staff and stakeholders. The organization operates as one of 20 subsidiaries under Nigerian National Petroleum Company Limited, focusing on non-energy business ventures.
Licensed by the National Health Insurance Authority, NNPC HMO provides private health insurance plans for corporate and retail clients across Nigeria’s six geopolitical zones. The organization launched a nationwide health insurance scheme in November 2025 covering over 7,000 petrol station attendants, significantly expanding its enrollment base beyond traditional NNPC employees.
The Alleged Breach Details
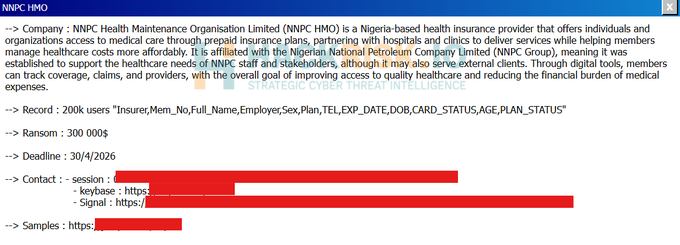
According to threat intelligence monitoring, XP95 posted their claim on dark web forums and Telegram channels on April 8, 2026. The group alleges they accessed systems containing 200,000 user records including names, dates of birth, phone numbers, email addresses, and potentially other Know Your Customer documentation typically collected by health insurance providers.
NNPC HMO has not issued any public statement confirming or denying the breach. Neither the Nigeria Data Protection Commission, the National Health Insurance Authority, nor NNPC Limited has released official comment on the incident as of this writing.
The XP95 Pattern Emerges
XP95 represents a relatively new player in the cyber-extortion landscape, first emerging in March 2026. The group’s name appears derived from legacy Microsoft operating systems — Windows XP and Windows 95 — reflected in their dark web leak site’s retro interface design.
Security researchers have tracked XP95 to several high-profile attacks in recent weeks, primarily targeting government agencies and public sector organizations in South Africa. The group breached Statistics South Africa, demanding $100,000 ransom for 154GB of data containing 453,362 files from the agency’s HR recruitment system. XP95 set an April 20, 2026 deadline for payment, threatening to publish the full archive if the ransom remains unpaid.
The threat actor also claimed responsibility for attacking Gauteng Provincial Government, alleging they obtained 3.8 terabytes of data containing 3.6 million files, which they offered for sale at $25,000. A separate breach of the Gauteng City Region Academy—a provincial skills development entity—resulted in XP95 claiming 147 gigabytes of stolen data with an identical $100,000 ransom demand.
Outside government targets, XP95 leaked data from Eholo Health, a Spanish psychological software provider, after the company allegedly refused to pay a $300,000 ransom demand. The group claimed Eholo valued patient data at only $80,000 and released the information publicly “to set a clear example for other companies that believe they can ignore serious breaches without consequences.”
Nigeria’s Expanding Data Breach Crisis
The alleged NNPC HMO breach arrives amid Nigeria’s escalating cybersecurity crisis. The country recorded over 119,000 data breaches in Q1 2025 alone, according to security reports. The Nigeria Data Protection Commission recently launched investigations into multiple major breaches affecting critical payment infrastructure.
On April 1, 2026, the NDPC served formal investigation notices to Remita Payment Services and Sterling Bank following allegations by threat actor bytetobreach of a massive 3TB data exfiltration affecting over 30 Nigerian organizations. That breach allegedly exposed 800GB of KYC documents, full database dumps, source code, and over 35,000 password hashes.
The NDPC’s investigation into the Remita-Sterling Bank breach came days after bytetobreach published portions of the stolen data on dark web forums, including sensitive government HSM keys and financial records. National Commissioner Vincent Olatunji warned that organizations deploying digital payment systems without adequate safeguards would face regulatory scrutiny under the Nigeria Data Protection Act 2023.
Healthcare Data Vulnerability
Health insurance providers hold particularly sensitive personal information—medical histories, treatment records, financial data, and government-issued identification. A breach of NNPC HMO’s systems, if confirmed, could expose enrollees to identity theft, medical fraud, and targeted phishing campaigns leveraging health-related information.
The organization’s ISO certifications (ISO 14001, 9001, and 45001) suggest established quality management and information security processes. However, certifications alone don’t guarantee immunity from sophisticated threat actors exploiting vulnerabilities in web-facing applications, misconfigured cloud storage, or compromised credentials.
Legal Obligations Under Nigerian Law
Nigeria’s Data Protection Act 2023 mandates strict breach notification requirements. Data controllers must notify the Nigeria Data Protection Commission within 72 hours of becoming aware of a breach likely to result in risk to individuals’ rights and freedoms. When breaches pose high risk, controllers must immediately communicate with affected data subjects in plain language, including mitigation advice.
For health-related data—classified as sensitive personal data under the Act—protection requirements are even more stringent. Organizations processing such information must implement appropriate technical and organizational measures, conduct Data Protection Impact Assessments, and maintain detailed processing records.
The National Health Insurance Authority also imposes regulatory obligations on accredited HMOs regarding patient data security and privacy protection.
What Users Should Do
While official confirmation from NNPC HMO remains pending, enrollees should take proactive security measures. Monitor health insurance accounts for unauthorized access or suspicious activity. Change passwords for NNPC HMO portals and any services sharing the same credentials. Activate Multi-Factor Authentication on all accounts containing personal or financial information.
Remain vigilant for phishing attempts referencing specific personal or health details—a common tactic following healthcare data breaches. Be cautious of unsolicited communications claiming to be from NNPC HMO or health providers requesting sensitive information or payment.
Watch for official breach notification letters, which the Data Protection Act requires organizations to send affected individuals. Contact NNPC HMO directly through verified channels if you have concerns about your data security.
A Pattern of Regulatory Silence
The prolonged silence from affected organizations following breach claims has become a concerning pattern in Nigeria’s cybersecurity landscape. Days often pass between public threat actor claims and official organizational responses, leaving users uncertain about their data security status.
This delay conflicts with the Data Protection Act’s 72-hour notification requirement and undermines public trust in digital services. For a health insurance provider handling sensitive medical and financial information for thousands of enrollees, transparency about potential data exposure isn’t optional—it’s legally mandated.
Until NNPC HMO, the Nigeria Data Protection Commission, or NNPC Limited issues official confirmation or denial, users should assume potential exposure and take appropriate defensive measures. The prudent approach is preparation rather than hope.
Follow us on Bluesky, LinkedIn, X, and Telegram to Get Instant Updates