Google, in collaboration with unnamed partners, dismantled the infrastructure of a hacking group it tracks as UNC2814, also known as Gallium. The disruption included terminating Google Cloud projects controlled by the attackers, disabling their internet infrastructure, and deactivating accounts used to access Google Sheets for command-and-control operations. According to Charlie Snyder, a senior manager with the Google Threat Analysis Group, the group had confirmed access to 53 separate entities across 42 countries, with potential access in at least 22 other nations at the time of the takedown.
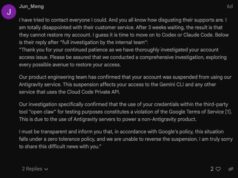
The hacking group utilized Google Sheets to manage its operations, a technique that allowed its malicious traffic to blend in with legitimate network activity, thereby evading detection. Google clarified that this method was an abuse of its platform’s features and not the result of a vulnerability in any Google product. In one identified case, the attackers installed a backdoor, which Google calls GRIDTIDE, on a compromised system containing sensitive personally identifiable information, including names, phone numbers, birth dates, and national ID numbers.
The disruption was initiated to halt what Google described as a “vast surveillance apparatus” targeting government and telecommunications organizations worldwide. In response to the announcement, Chinese Embassy spokesperson Liu Pengyu stated that cybersecurity is a “common challenge” and that China consistently opposes and combats hacking activities in accordance with the law, and at the same time firmly rejects attempts to use cybersecurity issues to smear or slander (the country).
Google noted this campaign is distinct from another high-profile group known as Salt Typhoon.
Google has issued notifications to all confirmed victims and is providing support to affected organizations. The disruption is expected to significantly degrade the hacking group’s operational capabilities, though security experts anticipate that the actors will likely attempt to rebuild their infrastructure. This incident highlights an increasing trend of threat actors abusing legitimate cloud services to conceal their activities.
Organizations are advised to monitor their networks for unusual API activity related to cloud services. Security teams should also implement robust access controls, regularly review account permissions, and use security tools capable of detecting anomalous patterns in network traffic that might indicate abuse of legitimate platforms for command-and-control communications.
Follow Hashlytics on Bluesky, LinkedIn , Telegram and X to Get Instant Updates