The Nigeria Data Protection Commission has announced an investigation into the alleged data breach affecting Remita Payment Services Ltd., Sterling Bank, and other entities, five days after cybercriminal ByteToBreach publicly leaked over 3 terabytes of data from more than 30 Nigerian organizations. The April 5, 2026 press release confirms the Commission served Notice of Investigation on April 1, after threat intelligence platforms and security researchers had already verified the breach.
What NDPC Says It’s Investigating
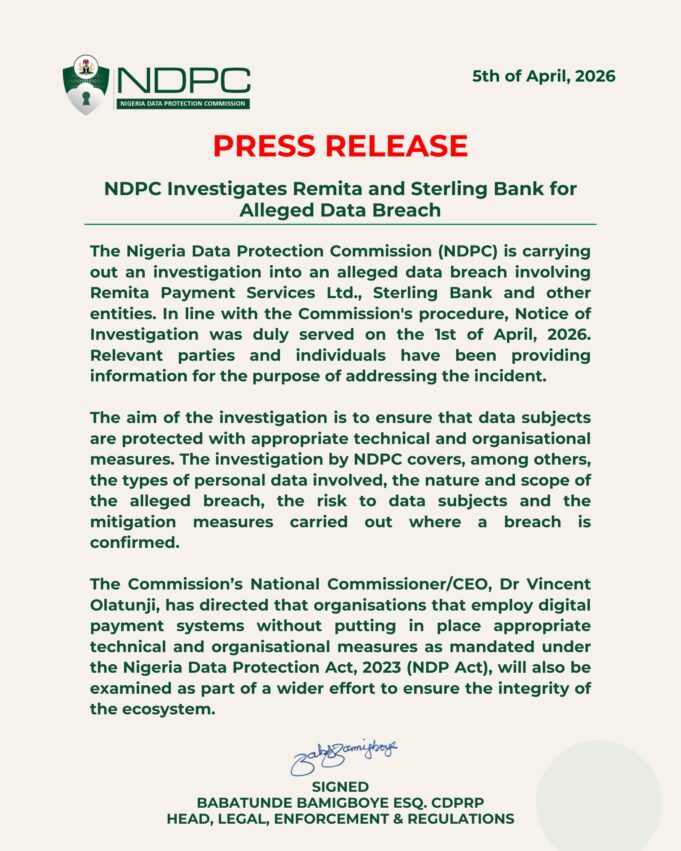
According to the official statement signed by Babatunde Bamigboye, Head of Legal, Enforcement and Regulations, the investigation will examine the types of personal data involved, the nature and scope of the alleged breach, the risk to data subjects, and mitigation measures carried out where a breach is confirmed. The Commission claims relevant parties and individuals have been providing information to address the incident.
National Commissioner and CEO Dr. Vincent Olatunji directed that organizations employing digital payment systems without appropriate technical and organizational measures mandated under the Nigeria Data Protection Act 2023 will also be examined as part of a wider effort to ensure ecosystem integrity.
The Timeline Problem
The Data Protection Act 2023 requires data controllers to notify the NDPC within 72 hours of becoming aware of breaches likely to result in risk to individuals’ rights and freedoms. ByteToBreach’s dark web post claiming the Remita breach appeared in late March 2026, with Sterling Bank’s 900,000 account compromise announced March 27. VECERT Analyzer publicly detected and reported the breach on March 31.
The NDPC served its Notice of Investigation on April 1 — at minimum, days after public disclosure, and possibly weeks after the breach occurred. Neither Remita nor Sterling Bank issued mandatory breach notifications to affected customers during this period. The Commission’s April 5 press release marks the first official acknowledgment, coming after the data had already been distributed across VPS servers, Google Drive, Dropbox, and Sync.
What The Investigation Should Find
The confirmed data exposure includes 800GB of KYC documentation with passports, national IDs, photographs, bank statements, and utility bills. Complete MySQL and Postgres database dumps containing financial transaction records are publicly accessible. Over 35,000 password hashes were released for free on dark web forums. Government Hardware Security Module keys that protect cryptographic operations have been exposed.
Sterling Bank’s servers served as the initial attack vector, which ByteToBreach used to pivot into Remita’s Amazon S3 storage infrastructure. The breach extended beyond these two entities to include Zenith Bank, Oyo State Government, Leadway Assurance, GetBumpa, Ahmadu Bello University Zaria, and over 25 additional government institutions, educational bodies, and commercial enterprises.
The Regulatory Failures
The investigation announcement itself highlights the compliance gap. The Act requires not just NDPC notification within 72 hours, but immediate communication to affected data subjects when breaches pose high risk. As of April 5, no mass breach notification has reached the 900,000 Sterling Bank customers whose accounts were compromised, nor the millions of Nigerians whose KYC documents now circulate on criminal forums.
The NDPC’s statement uses language like “alleged breach” and “where a breach is confirmed” despite public availability of the stolen data and verification by multiple independent security researchers. The investigative posture—gathering information from relevant parties—comes after the critical window for damage control has closed.
What Nigerians Still Aren’t Being Told
Neither Remita nor Sterling Bank has publicly confirmed the breach, disclosed the number of affected customers, or provided specific mitigation steps. The NDPC announcement offers no guidance to potentially impacted individuals beyond stating that the investigation aims to ensure data subjects are protected. There’s no hotline, no victim assistance program, no official list of compromised organizations.
The statement promises to examine organizations employing digital payment systems without appropriate security measures, but doesn’t address the immediate crisis: millions of Nigerians whose personal identification documents, financial records, and passwords are now weaponized tools for identity thieves and fraudsters.
The Broader Implication
Nigeria recorded over 119,000 data breaches in Q1 2025 alone. The Central Bank mandated cybersecurity self-assessments for all banks on March 30, 2026—one day before the NDPC served its Notice of Investigation, and days before publicly acknowledging the breach. This disconnect between regulators, the magnitude of the incident, and the glacial public response raises questions about whether Nigeria’s data protection framework can function during actual crises.
The NDPC statement notes it will examine ecosystem integrity and appropriate technical measures. But the fundamental breach of the regulatory compact has already occurred: data controllers failed to secure sensitive information, failed to detect massive exfiltration, failed to notify regulators within legal timeframes, and failed to warn affected citizens before their data became public.
What Happens Next
The NDPC investigation will determine whether to impose penalties under the Data Protection Act, which provides for substantial fines and enforcement actions against non-compliant organizations. Previous actions by the Commission include the August 2025 probe of over 1,000 organizations for data protection violations, though enforcement outcomes from those investigations remain unclear.
For the millions of Nigerians whose data is already compromised, the investigation announcement changes nothing. The 800GB of KYC documents, financial records, and password hashes are already in criminal hands. Identity theft, fraudulent loans, and targeted phishing campaigns are already underway. The regulatory response arrived after the damage was done.
The NDPC’s five-day delay between public breach disclosure and official acknowledgment may itself warrant scrutiny. When the Commission that exists to protect data subjects learns about catastrophic breaches from dark web forums and security researchers rather than from legally obligated data controllers, the entire regulatory framework has failed its fundamental purpose.
Follow us on Bluesky, LinkedIn, X, and Telegram to Get Instant Updates