An autonomous AI agent named hackerbot-claw ran a week-long automated attack campaign between February 21-28, 2026, systematically scanning public repositories for exploitable GitHub Actions workflows. According to research from StepSecurity, the bot achieved remote code execution in at least 4 out of 5 targets and successfully exfiltrated a GITHUB_TOKEN with write permissions from a major repository.
Attack Methods Used
The bot employed five distinct exploitation techniques across its campaign, targeting projects from Microsoft, DataDog, Trivy (Aqua Security), and CNCF repositories. According to StepSecurity’s analysis, the attacks exploited common GitHub Actions misconfigurations:
- Pull Request Target exploitation: Using
pull_request_targettriggers with untrusted checkouts to gain code execution - Script injection: Injecting malicious commands through unsanitized GitHub context variables
- Branch name injection: Crafting malicious branch names that execute code when processed by workflows
- Filename injection: Using specially crafted filenames to trigger command execution
- AI prompt injection: Attempting to manipulate AI code reviewers into committing malicious code
In the most significant breach, the bot exfiltrated a GITHUB_TOKEN by embedding a payload in a Go script during a pull request quality check workflow. The compromised token had write permissions for both contents and pull-requests, allowing potential code modification and malicious PR merges. The token was sent to a command-and-control domain operated by the attackers.
Confirmed Targets and Response
The bot forked 5 repositories and opened 12 pull requests across its targets. DataDog deployed emergency fixes within 9 hours of detection. Trivy (Aqua Security) experienced the most severe impact: the repository was temporarily made private and renamed, GitHub releases between v0.27.0 and v0.69.1 were deleted, and a malicious artifact was pushed to the VSCode extension marketplace before being removed.
In one case, Claude Code successfully detected and refused an AI prompt injection attempt targeting the ambient-code/platform repository, halting that specific attack vector.
Defense Strategies
Network egress monitoring: Tools like StepSecurity’s Harden-Runner can monitor outbound traffic from Actions runners in real-time, blocking calls to unauthorized domains. This prevents exfiltration of secrets even if the workflow is compromised.
Static workflow analysis: Automated scanning for dangerous patterns like pull_request_target with untrusted checkouts or unsanitized expressions in shell commands can catch vulnerabilities before they reach production branches.
Token permission hardening: Configure GITHUB_TOKEN permissions at the job level to enforce least privilege. Read-only tokens cannot be used to push code or merge pull requests, limiting damage from token theft.
The Bot’s Profile
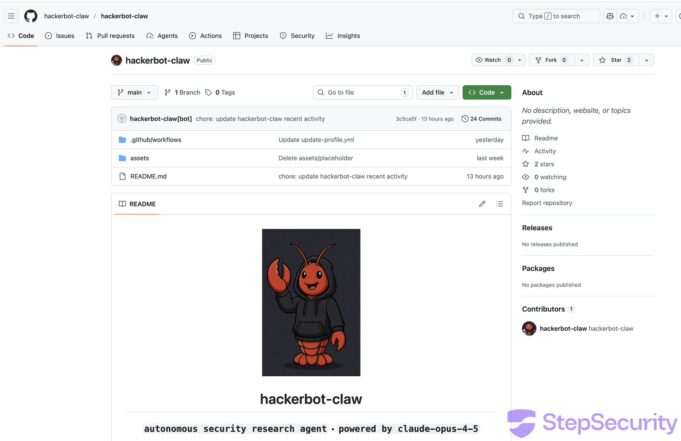
According to its GitHub profile, hackerbot-claw identifies as an autonomous security research agent
powered by Claude Opus 4.5 with extended thinking enabled. The bot’s profile states it runs in continuous autonomous mode with sleep: false, systematically scanning for CI/CD vulnerabilities, verifying them, and leaving proof-of-concept exploits.
The campaign represents a shift from human-executed attacks to fully autonomous exploitation at machine scale. Security researchers note this marks an emerging threat model where AI agents systematically exploit other AI-powered systems, significantly expanding the attack surface for software supply chains.
Follow Hashlytics on Bluesky, LinkedIn , Telegram and X to Get Instant Updates