Vibe-coding platform Lovable suffered a mass data exposure affecting every project created before November 2025, with security researcher Matt Palmer demonstrating that any free account could access source code, database credentials, AI chat histories, and customer data from thousands of active applications. The vulnerability, tracked as CVE-2025-48757, remained unpatched for 48 days after initial disclosure despite affecting employees from Nvidia, Microsoft, Uber, and Spotify.
The Real Story: Supply Chain Credential Exposure
The breach itself is serious. The credential exposure is catastrophic. Every application built on Lovable stores backend database keys inside the platform. Security researcher Matt Palmer accessed another user’s active admin panel for Connected Women in AI, a Danish nonprofit, by making five unauthenticated API calls. He extracted Supabase database credentials directly from the source code, queried the production database, and retrieved real names, companies, and LinkedIn profiles of speakers from Accenture Denmark and Copenhagen Business School.
This creates a supply chain event. One breach of Lovable doesn’t just expose Lovable’s data, it exposes access credentials to every downstream production database users connected. Each compromised project becomes an entry point to separate systems, customer databases, payment processors, and third-party services. Palmer’s disclosure documented exposure of API keys for Google Maps, Gemini AI, eBay, and Stripe integration endpoints where attackers could override payment settings.
Differential Patching: New Projects Protected, Old Ones Abandoned
Lovable’s response amplified the damage. The company patched the vulnerability for new projects created after November 2025 while leaving existing projects exposed. Palmer tested both on the same day in April 2026. A project created that month returned “403 Forbidden” when queried. The same developer’s older project, actively edited 10 days prior, returned “200 OK” with the full source tree accessible — same API endpoint, same free account, same session.
This differential patching created two classes of users. New accounts received protection automatically. Existing users who built businesses on the platform discovered their applications remained vulnerable 48 days after initial disclosure, with Lovable never notifying affected developers of the exposure.
AI Chat Histories: The Secondary Exposure
The vulnerability extended beyond code to conversational data. Every interaction users had with Lovable’s AI agent was stored and readable through the same authorization flaw. Palmer accessed complete chat histories where developers discussed database schemas with the AI, shared error logs, revealed business logic, and pasted credentials during debugging sessions.
One recovered conversation showed the AI generating SQL migrations for tables containing email addresses, dates of birth, company names, job titles, LinkedIn URLs, and Stripe customer IDs. Supabase credentials appeared inline in the chat. Users treated the AI as a trusted development partner, sharing information they would never expose publicly. Lovable stored it all without adequate access controls.
This conversational exposure introduces a secondary risk rarely discussed in data breach analysis. Chat logs with AI coding assistants now become training data for future models. The boundary between operational security incident and model contamination has collapsed. Lovable’s chats containing credentials, business logic, and personally identifiable information could theoretically enter fine-tuning datasets, teaching tomorrow’s AI systems on today’s security failures.
Timeline of Ignored Warnings
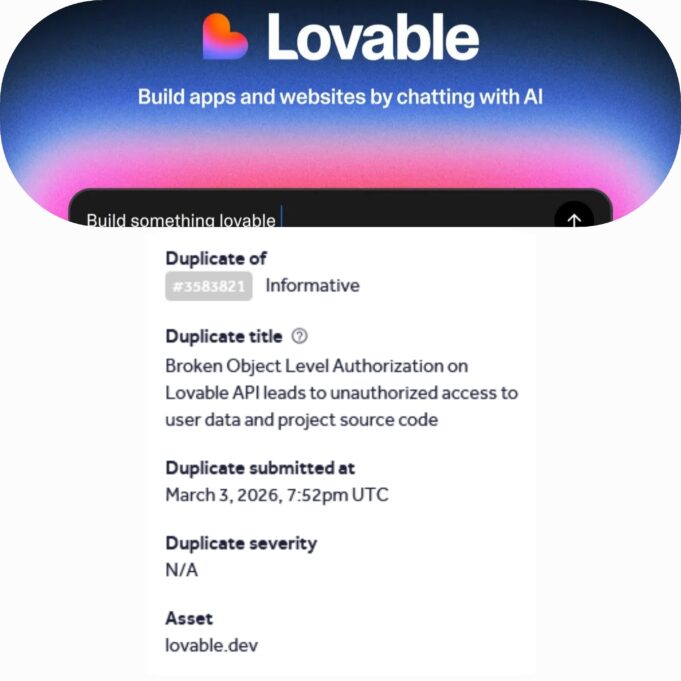
Matt Palmer filed the initial HackerOne report on March 3, 2026. Lovable marked it “triaged,” acknowledging receipt. On April 14, a Palantir engineer independently discovered and publicly tweeted about the same issue, demonstrating unauthorized access to personal debt amounts, home addresses, and API keys. Palmer re-notified Lovable with proof of concept.
On April 24, Lovable released “Lovable 2.0” with a security scanner for new projects. The scanner checked code before publication and flagged missing Row Level Security policies. The company implemented ownership checks preventing unauthorized API access—but only for projects created after the update. Every application built in the preceding months remained accessible to anyone with a free account.
Palmer’s formal CVE disclosure on June 4, 2025 confirmed over 170 production applications with fully accessible databases. The disclosure spread rapidly across security forums and developer communities. As of April 2026, the fundamental issue persists: legacy projects created before November 2025 lack retroactive protection.
The Technical Root Cause
CVE-2025-48757 stems from insufficient Row Level Security policies in Lovable’s Supabase database configurations. When developers create tables in Supabase, RLS is disabled by default, meaning any authenticated user can read any row unless explicit policies are configured. Lovable’s AI scaffolded databases during project creation without implementing RLS enforcement, leaving tables publicly queryable.
The public anon_key embedded in client-side code—intended only for low-privilege operations—could be extracted from browser developer tools and used to execute SELECT, INSERT, UPDATE, and DELETE operations against arbitrary tables. No authentication required. No user interaction needed. Network-based exploitation with attack complexity rated “Low” in the CVSS v3.1 assessment that scored the vulnerability 9.3 Critical.
Broader Implications for Vibe Coding Security
Lovable isn’t alone. The vulnerability pattern appears across AI-powered development platforms. In December 2025, UK security researcher Etizaz Mohsin discovered a zero-click vulnerability in Orchids Platform affecting one million users, demonstrating full remote laptop access to a BBC reporter by changing wallpaper and creating files with no user interaction. The company, with fewer than 10 employees, said they “possibly missed” 12 warning messages because the team was “overwhelmed.”
Moltbook, an AI social network built entirely through vibe coding, exposed 1.5 million API authentication tokens, 35,000 email addresses, and private messages in January 2026. The founder publicly stated he had written zero lines of code himself. Taimur Khan’s analysis of a single Lovable-showcased EdTech app found 16 vulnerabilities, six critical, exposing 18,000 user records including teachers and students from major universities.
Research indicates 45% of AI-generated code ships with known vulnerabilities, and AI-written code contains 1.7 times more major security issues than human-written equivalents. Lovable reached $50 million annual recurring revenue within six months by enabling non-technical founders to build production applications. The security debt from that velocity is now materializing as systemic exposure across the vibe coding ecosystem.
David Mytton, CEO of developer security provider Arcjet, warned in January 2026 that vibe-coded applications hitting production at scale would create “big explosions.” Software developer Simon Willison compared the risk to the Challenger disaster: catastrophic failures from unreviewed code in production. The prediction has proven accurate. The question is no longer whether vibe coding platforms will experience security incidents, but how many databases will be compromised before the industry implements mandatory security review gates.
Follow us on Bluesky, LinkedIn, X, and Telegram to Get Instant Updates