Microsoft Edge decrypts every stored password into process memory the moment the browser launches and retains them as cleartext for the entire session, regardless of whether users visit the associated websites. Security researcher Tom Jøran Sønstebyseter Rønning disclosed the behavior April 29, 2026 at PaloAlto Networks Norway’s BigBiteOfTech conference after systematically testing every major Chromium-based browser. Edge was the only one that exhibited this credential handling approach. When notified, Microsoft’s official response classified the behavior as “by design,” stating that access to browser memory would require the device to already be compromised.
How Edge’s Memory Handling Differs From Chrome and Firefox
Google Chrome implements on-demand decryption—credentials only surface in plaintext during autofill or when a user explicitly views a saved password in settings. Chrome’s App-Bound Encryption (ABE) adds a second layer of protection by cryptographically locking decryption keys to an authenticated Chrome process running as SYSTEM. This prevents other processes from reusing those keys even if they gain memory access. Firefox employs similar on-demand decryption without preloading the entire password vault.
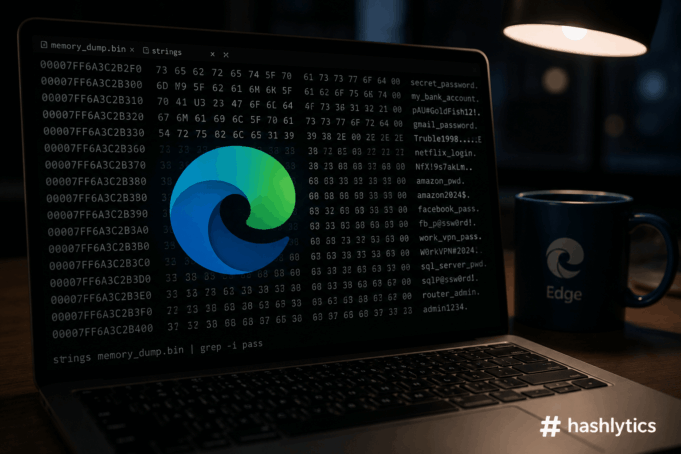
Edge’s approach loads all passwords into memory at startup, creating a persistent attack surface. On shared Windows environments—terminal servers, virtual desktop infrastructure, enterprise workstations with multiple logged-on users—the implications escalate. Rob VandenBrink at SANS Institute Security Center demonstrated the exploit’s simplicity: open Edge without browsing anywhere, navigate to Task Manager, expand the Edge task, right-click the “browser” sub-task, select “Create Memory Dump,” and search the resulting file with Sysinternals Strings tool. Every credential appears in plaintext.
The logged-in Windows user can execute this process with no additional privileges. Any malware that user runs inherits the same access. Rønning’s proof-of-concept video showed an attacker with admin rights on a terminal server reading memory from two other logged-on users — one actively using Edge, one disconnected but with Edge running in the background. Both users’ complete password vaults were accessible.
The Security Theater of Edge’s Authentication Prompt
Edge demands biometric or password re-authentication before revealing saved credentials through its Password Manager UI. Users see this security gate as protection—proof that accessing stored passwords requires additional verification. But that interface-level authentication protects nothing when the browser process already holds every credential in plaintext memory from the moment Edge launched.
Danwei Tran Luciani, chief product technology officer at application security firm Detectify, told Dark Reading the contradiction creates false security expectations. The product signals one protection level while operating at another. Users believe their passwords are secured behind authentication prompts, unaware that memory scraping bypasses those controls entirely. Privacy protections that appear functional but fail under examination aren’t new in consumer technology, but browser password storage carries direct financial and account access consequences when compromised.
Microsoft’s Defense and Why It Falls Short
Microsoft’s statement to press outlets maintained that “access to browser data as described would require the device to already be compromised” and that “design choices involve balancing performance, usability, and security.” The company framed cleartext memory storage as necessary for helping users “sign in quickly and securely — this is an expected feature of the application.”
The “already compromised” argument dismisses legitimate threat models where Edge’s behavior meaningfully worsens outcomes. Infostealer malware operates with user-level privileges, not admin access. When users execute infected files, open malicious attachments, or run compromised software, the malware inherits their permissions—sufficient to dump Edge’s memory and exfiltrate the password vault. Chrome’s App-Bound Encryption raises the bar by requiring attackers to compromise SYSTEM-level processes, a significantly harder target than user-space memory access.
Terminal server environments demonstrate another scenario Microsoft’s response doesn’t address. Multiple users share a single Windows Server instance via Remote Desktop Services. Admin-level access on that server grants visibility into all user processes. An attacker compromising an admin account can scrape Edge memory from every logged-on user simultaneously. Chrome’s ABE design limits this attack by isolating credential access to authenticated browser processes rather than exposing them to any admin-level memory reader.
The “performance and usability” justification conflicts with Chrome’s implementation. Chrome decrypts on-demand and maintains ABE protections without users reporting performance degradation or authentication friction. If Google can balance security and usability without preloading cleartext passwords, Microsoft’s design choice appears less about technical necessity and more about development priorities.
Why This Matters Beyond Individual Users
Enterprise environments deploying Edge through Group Policy face credential exposure risks that third-party password managers with master passwords partially mitigate. Organizations running virtual desktop infrastructure, shared workstations, or terminal servers where multiple users access systems should treat Edge’s cleartext memory handling as high-priority configuration risk. The 2023 shift in Microsoft’s security guidance recommended using Edge’s built-in password manager over disabling it, based on “new features that altered security tradeoffs.” That recommendation predates the April 2026 cleartext memory disclosure.
The finding also highlights broader browser security posture differences relevant to device security strategies. Apple’s automatic Stolen Device Protection demonstrates platform-level credential safeguards. Samsung Wallet security updates and WhatsApp’s biometric passkey implementation reflect industry movement toward additional authentication layers for sensitive data. iOS payment autofill expansion includes tokenization and device-bound authentication that Edge’s cleartext approach doesn’t match.
Microsoft maintains extensive enterprise security documentation, but the cleartext memory decision undermines defense-in-depth principles. When credentials become accessible through simple memory dumps requiring no exploit code, no privilege escalation, and no complex attack chains, organizations lose the layered protection model that makes compromise detection and response feasible.
What Users and Organizations Should Do
Individual users storing sensitive credentials — banking, email, work accounts — in Edge should migrate to dedicated password managers requiring master passwords for decryption. Bitwarden, 1Password, and KeePassXC don’t load password vaults into memory until the master password is provided, and they implement memory protection techniques Edge lacks. After migrating credentials, delete all passwords from Edge’s built-in manager to eliminate the cleartext exposure surface.
Enterprise IT teams should evaluate whether Edge’s credential handling aligns with organizational risk tolerance. For environments where Edge is mandatory, disable the built-in password manager via Group Policy and mandate third-party solutions with master password requirements. Document the cleartext memory behavior in risk assessments and security architecture reviews—auditors and compliance frameworks increasingly scrutinize browser-level data protection.
Security operations centers monitoring for credential theft should add Edge memory dump patterns to detection rules. Tools like Sysinternals Process Monitor can log memory dump operations. While false positives occur in legitimate debugging scenarios, unexpected memory dumps of browser processes warrant investigation, particularly in shared or high-value user environments.
For organizations that cannot immediately migrate away from Edge’s password manager, implement compensatory controls. Enforce multi-factor authentication universally, reducing the value of stolen passwords. Deploy endpoint detection and response platforms with memory protection capabilities. Segment network access so compromised credentials provide limited lateral movement opportunities.
Browser Security as Infrastructure Decision
The Edge cleartext password revelation isn’t just a technical vulnerability—it’s a design philosophy difference. Chrome prioritized credential protection through on-demand decryption and cryptographic process binding. Firefox followed similar principles. Edge chose performance convenience over attack surface minimization, betting that “device already compromised” scenarios fall outside their threat model.
That bet fails in real-world enterprise environments where admin access exists legitimately, shared systems create multi-user credential exposure, and infostealer malware operates at user privilege levels sufficient to dump browser memory. Microsoft’s “by design” response suggests no immediate change is planned, leaving organizations to decide whether Edge’s credential handling meets their security requirements or whether browser choice itself becomes a security control.
The finding underscores that browser selection carries security implications beyond feature sets and performance benchmarks. When a browser loads every saved password into cleartext memory at startup, password managers become credential broadcast systems waiting for memory readers. Organizations treating browser deployment as mere user preference rather than infrastructure security decision should reconsider that posture in light of Edge’s approach to credential protection—or more accurately, the lack thereof.
Follow us on Bluesky, LinkedIn, X, and Telegram to Get Instant Updates